Nikesh Arora, Chief Executive Officer of Palo Alto Networks.

Instead of winding down at the end of the year, already strapped security teams were scrambling over the last week to ensure their organisations are safe in the wake of the SolarWinds disclosure. Attackers got in via a compromise of the Orion software build system, up to 18,000 customers of SolarWinds then unknowingly let them in. As the world focuses on the growing list of organisations that have been compromised, there’s also a growing list of those that believe they’re ok.
Many have taken the approach that if they are not running SolarWinds, or a particular version of it, then they can go back to business as usual. I saw a security researcher post a picture of a whisky glass with ice and a cigar recommending other security folks to take a break, because he was fearful this could be a long winter.
There is something wrong with this picture. Cyber activity is going to go up, not down. If we all thought cybersecurity was important before, 2020 made it more so. Your brick and mortar store is closed, your employees are all connecting from home, your entire business just went digital.
Against this backdrop, SolarWinds has exposed infrastructure weaknesses in organisations. It’s amazing how many were struggling this week to figure out where they were running related products, and how many, and which were affected. Next time it shouldn’t take us so long.
My message isn’t for the companies that confirmed they were breached, it’s for those who are celebrating they dodged this bullet. This is a wake up call to modernise cybersecurity. There are immediate areas that organisations need to focus on to prepare.
It’s critical that organisations understand their environments with a complete, accurate, up-to-date baseline. This means moving beyond simply checking if they run SolarWinds. Too many organisations don’t know all that they have, and not all they have is updated to the most recent versions, ironically, saving thousands of SolarWinds customers who were slow to download the tainted update. You don’t want to be spending days of your critical incident response time just figuring out what your inventory is. Organisations need to immediately complete a detailed analysis of their entire systems, infrastructure, software, supply chains and external attack surface. Nimble organisations will not only detect and prevent these attacks in the future, but with this baseline, be able to conduct forensic investigations rapidly.
Fix our infrastructure for real. Enterprise IT architectures need to have all logging, network, and security data talking to each other, with software smart enough to identify useful things within those data. This campaign could have been stopped sooner if products were more integrated. Organisations need to pivot to a cybersecurity platform that can detect and correlate millions of events across hosts, networks, firewalls and clouds in realtime, then implement comprehensive detection and response. Hackers use highly efficient tools and methodologies; organisations need to embrace the efficiency of a cybersecurity platform powered by machine learning to keep up.
Here’s why it matters. Technology is about all that went right in 2020. When the pandemic moved in, remote access kept businesses and governments moving. Retailers went digital as it was the only way to survive. But that means we are protecting an ever-expanding perimeter, against attacks that get more and more sophisticated.
The attack by the group we call SolarStorm joins the list of cybersecurity watersheds: massive DDoS attacks and cyber heists affecting our financial services infrastructure, wiper attacks that crippled corporations and energy production, the theft of classified secrets from governments and the NotPetya attack that shut down ports, pharmaceutical factories and manufacturing and cost corporations billions of dollars of losses.
100% prevention, 100% of the time is impossible. At some point you have to trust vendors and the security updates they provide. But against bad guys who are always attempting to out-innovate us, security has to be more proactive and future-proof: If you were not able to prevent an attack in realtime, you need to detect and investigate near realtime. The days of fragmented security and lengthy investigation cycles are behind us, we need good data and real world AI to get ahead.
Now is not the time to breathe a sigh of relief that you’re not impacted. Sophisticated hackers spend years planning campaigns, we must devote similar resources to our defences. Let’s prepare to prevent the one that’s inevitably unfolding now, so we’re not scrambling to retrace what happened.
Brief background
It is one of the biggest cyberattacks against organisations and government entities around the world. While its epicentre is in the US, the shockwaves have rippled across the world and even reached UAE shores. Dubbed the SolarWinds hack, the attack is thought to be state-sponsored.
The existence of the SolarWinds hack was first reported on December 8, by the security firm FireEye, and since then the roster of victims has been growing steadily as more organisations have been reporting the presence of related malware on their networks. The list already includes the US Treasury, Department of Homeland Security, Department of Commerce and various departments of the Pentagon.
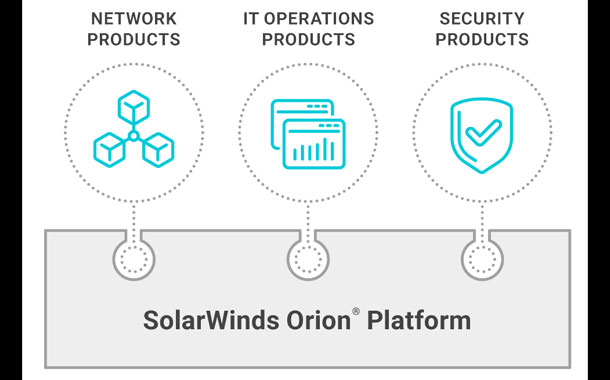
The hack was traced back to trojanised updates released for the SolarWinds Orion software, which is a network monitoring platform used by 33,000 companies around the world, including 425 on the Fortune 500 list. SolarWinds estimates the hack has impacted 18,000 companies.
Meanwhile, Microsoft has released a statement noting that more than 40 of its customers have been impacted. 80% of these are in the USA, while the remaining are spread across Canada, Mexico, Belgium, Spain, the UK, Israel, and the UAE.
The US Department of Homeland Security has issued an emergency directive to all federal government agencies. It notes that the exploitation of SolarWinds products poses an “unacceptable risk” to Federal Civilian Executive Branch agencies and requires emergency action. The hack has a high potential for a compromise of agency information systems. “Affected agencies shall immediately disconnect or power down SolarWinds Orion products, versions 2019.4 through 2020.2.1 HF1, from their network. Until such time as CISA directs affected entities to rebuild the Windows operating system and reinstall the SolarWinds software package, agencies are prohibited from joining or rejoining the Windows host OS to the enterprise domain.”
A joint statement released by US authorities underlines the severity of the attack. In it, the FBI, the Cybersecurity and Infrastructure Security Agency, CISA, and the Office of the Director of National Intelligence, ODNI, acknowledge the formation of a Cyber Unified Coordination Group, UCG, to coordinate a whole-of-government response to this significant cyber incident. The UCG is intended to unify the individual efforts of these agencies to understand the full extent of the attack.
Security agencies have also unearthed a second threat actor that has exploited the SolarWinds software to insert malware into corporate and government networks. Apparently, this attack group is not related to the suspected Russian government-backed group responsible for the first SolarWinds hack.
The story is still developing, and on this page, we will be posting comments and advisories as they come in. So go ahead and bookmark this link.
Costin Raiu, Director, Global Research and Analysis Team, Kaspersky.

While studying the Sunburst backdoor, Kaspersky’s experts discovered a number of features that overlap with a previously identified Kazuar. Which is a backdoor written using the .NET framework first reported by Palo Alto in 2017 and used in the cyberespionage attacks across the globe. Multiple similarities in code suggest a connection between Kazuar and Sunburst, albeit of undetermined nature. The overlapped features between Sunburst and Kazuar include the victim UID generation algorithm, the sleeping algorithm and the extensive usage of the FNV-1a hash. According to the experts, these code fragments are not 100% identical, suggesting Kazuar and Sunburst may be related, though the nature of this relation is still not entirely clear.
After the Sunburst malware was first deployed, in February 2020, Kazuar continued to evolve and later 2020 variants are even more similar in some respect to Sunburst. Overall, during the years of Kazuar evolution, the experts observed a continuous development, in which significant features which bear resemblance to Sunburst, were added. While these similarities between Kazuar and Sunburst are notable, there could be a lot of reasons for their existence, including Sunburst being developed by the same group as Kazuar, Sunburst developers using Kazuar as an inspiration point, the move of one of Kazuar developers to the Sunburst team, or both groups behind Sunburst and Kazuar having obtained their malware from the same source.
The identified connection does not give away who was behind the SolarWinds attack, however, it provides more insights that can help the researchers move forward in this investigation. Kaspersky believes it’s important that other researchers around the world investigate these similarities and attempt to discover more facts about Kazuar and the origin of Sunburst, the malware used in the SolarWinds breach. Judging from past experience, for instance, looking back to the WannaCry attack, in the early days, there were very few facts linking them to the Lazarus group. In time, more evidence appeared and allowed us, and others, to link them together with high confidence. Further research on this topic is crucial for connecting the dots.
Ray Kafity, Vice President, Middle East Turkey and Africa at Attivo Networks

The SolarWinds incident is a reminder that no one is invincible to a determined cyber threat actor. The breach originated from a trojanised update to the IT monitoring and management software, allowing access via a backdoor. SolarWinds revealed that there were traces of the attackers’ activity dating back to Oct 2019. Given enough time, skilled attackers always escalate privileges and move laterally to compromise sensitive data and intellectual property. Attackers reportedly used this attack to breach FireEye and exfiltrate their Red Team tools for security assessments; compromised email servers to monitor internal email traffic at the US Treasury and Commerce departments, and likely, many more organisations. This attack had the potential to impact an incredible 18,000 organisations.
It’s important to note that the attacker remained undetected in the network for so long due to the absence of any measures to detect lateral movement. Most cybersecurity solutions rely on detecting signatures and matching patterns from previous attacks, which tend to be limited in their effectiveness. Solutions that utilise other techniques, such as those developed by Attivo Networks, make prevention and detection much more effective and reliable.
In this scenario where the attacker was most likely creating beachheads in environments outside of SolarWinds, detection inside the network is key to containing and eradicating the threat. Potentially affected organisations must seriously consider that in the event that dormant backdoors reopen how long it will take them to detect lateral movement or privilege escalation.
What they need is eyes inside the network. The Attivo Networks ThreatDefend platform and Endpoint Detection Net Suite use various strategies, including deception and concealment technologies, to detect and prevent such evasive attack tactics at very early stages. These strategies act as a failsafe to catch attackers by surprise once they infiltrate the organisation’s network and attempt to move laterally. The solution assumes that attackers are already inside the network, so it looks for specific activities they would conduct as they move deeper into the environment, resulting in very high-fidelity alerts.
In response to this breach event, Attivo Networks announced immediate free access to their endpoint protection products for customers keen to tighten their security protocols and prevent attackers from progressing inside the network and remaining undetected.
Morgan Wright, Chief Security Advisor, SentinelOne

One caveat: this is very early in the damage assessment. As with any network compromise, it might take months to uncover the information needed to provide proper attribution and develop countermeasures.
This attack targeted more than the federal government, so the damage will be far reaching. Based on the available information, the attackers, Russia SVR based on other reporting, initially compromised SolarWinds, a network management software application used by many in the government, defence industrial base, and private sector.
Instead of attacking hundreds of targets, the technique was to attack one target that serviced hundreds of customers. By piggybacking their malware on the updates from SolarWinds, this made the malware appear to be trusted because SolarWinds and their updates were trusted.
This is very similar to the type of attack Russia carried out against Ukraine and their energy grid back on December 23, 2015. The BlackEnergy malware also had a first-of-a-kind tradecraft, which was operation specific malicious firmware updates that targeted the serial-to-ethernet adaptors used to open/close breakers at the energy plants. This is very consistent with the current tradecraft.
This attack reinforces the need to upgrade legacy protection schemes and techniques to modern, behaviour-based types of approaches. A single solution will never solve all problems. Rather, modernisation of the IT infrastructure and AI-based defence will at least level the playing field. The attackers always have the advantage, but we can change that by detecting and responding at machine speeds.
Sam Curry, Chief Security Officer, Cybereason

News of a breach with the potential size of the one carried out on the U.S. Treasury and Commerce Departments is eye opening and of big concern. In addition, the directive from the Cybersecurity and Infrastructure Security Agency urging all public and private sector companies to assess their exposure to the massive hack and plea to disconnect or power down SolarWinds products is exceedingly infrequent. Quite frankly, I am shocked. People need to pay attention to this directive and respond. Not later today or tomorrow, but now.
The good news is that the infrequency of these types of directives will catch everyone’s eye and reinforce the seriousness of this latest breach. In other words, this warning should not go unnoticed. Since SolarWinds has tens of thousands of customers and more than 400 out of the world’s Fortune 500, a bold action like this was needed and required across the public and private sector.
Amazingly, this directive is the first of this scale that we have seen in 2020. Now we all want to know what the private sector companies protected in part by SolarWinds will do. We should all be listening carefully to SolarWinds as well. As defenders, their first job is protecting their clients, but they hold vital pieces of information as well. Their transparency and openness is extremely important. Playing the victim card in these instances is unacceptable. In the short term for any customers of SolarWinds it is time to create a task force or war room to hunt adversaries and deal with the specific TTPs, vulnerabilities and exploits in question.
Let us all remember the fog of cyber way makes things in the moment very hard to tell and difficult to assess, but over time, whether its days, weeks or months it will become clear. Today, this is a security drill that no one wants as 2020 gets in its parting shots. As public and private sector companies share common tools, practices and managed services, it is important to remember that homogeneity can make us vulnerable and these threats can spread like wildfire if not dealt with immediately.
With the U.S. government looking to transition between administrations, cyber activity that leads to lockdowns and freezes has the potential to slow or damage government transition work. With the inauguration in January, it is important that first we do not allow any damage, but also after that the government can proceed in its normal transition of administrations.
Ammar Enaya, Regional Director – METNA, Vectra

This is a significant example of a well-executed supply chain attack compromising a popular IT administration tool as a penetration mechanism. The subsequent exploitation of authentication controls enabled the threat actor to pivot to the cloud and operate undetected for an extended time in Microsoft 365, which allowed them to gather intelligence. The US Government’s Cybersecurity and Infrastructure Security Agency has issued an Emergency Directive calling on all US federal civilian agencies to review their networks for indicators of compromise and disconnect or power down SolarWinds Orion products immediately.
As organisations increasingly become hybrid cloud environments, we’ve seen attackers focus on privileged access and the use of legitimate tools for malicious actions. For example, in a recent study of 4 million Microsoft 365 accounts, we identified that 96% of organisations exhibited lateral movement behaviours including multifactor authentication, and embedded security controls that are being bypassed. A threat actor can then, with a few clicks, reconfigure email rules, compromise SharePoint and OneDrive file stores, and set up persistent reconnaissance and exfiltration capabilities using built-in M365 tools such as eDiscovery and Power Automate.
Opportunities for these kind of attacks are vast and growing. It highlights the need for security teams to be able to tie together all host and account interactions, as they move between cloud and on-premise environments, in a consolidated view. Security teams also need to drastically reduce the overall risk of a breach by gaining instant visibility and understanding of who and what is accessing data or changing configurations, regardless of how they are doing it, and from where.