Discovered in December 2021, Log4Shell quickly became infamous as the vulnerability of the year. Although the Apache Foundation released a patch for this CVE shortly after its discovery, this vulnerability continues to pose a huge threat for individuals and organizations. In fact, during the first three weeks of January, Kaspersky products blocked 30,562 attempts to attack users using exploits targeting the Log4Shell vulnerability.
CVE-2021-44228 or Log4Shell is a Remote Code Execution (RCE) class vulnerability, meaning that if it is exploited on a vulnerable server attackers gain the ability to execute arbitrary code and potentially take full control over the system. This CVE has been ranked a 10 out of 10 in terms of severity.
The vulnerability is extremely attractive to cybercriminals because it allows them to gain complete control over the victim’s system and is easy to exploit.
Since it was first reported, Kaspersky products have detected and prevented 154,098 attempts to scan and attack devices through targeting the Log4Shell vulnerability. Most of the attacked systems were located in Russia (13%), Brazil (8.97%) and the USA (7.36%).
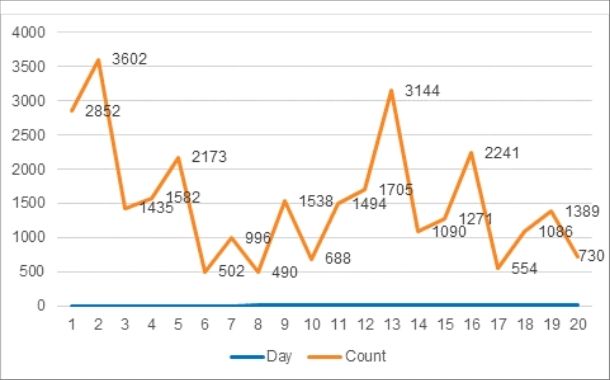
Although the Apache Foundation has already released a patch for this CVE, it takes weeks or months for vendors to update their software. Unsurprisingly, Kaspersky experts have observed that malicious attackers are continuing widespread scans to exploit Log4Shell. The first three weeks of January saw Kaspersky products block 30,562 attempts to attack users by means of targeting the Log4Shell vulnerability. Moreover, almost 40% of these attempts were detected within the first five days of the month, from 1-5 January.
“We certainly see that there have been far fewer scans and attempted attacks using Log4Shell than there were in the first weeks when it was initially discovered. Still, attempts to exploit this vulnerability are here to stay. As our telemetry shows, cybercriminals continue their extensive mass scanning activities and make attempts to leverage the exploitable code. This vulnerability is being exploited by both advanced threat actors who target specific organizations and opportunists simply looking for any vulnerable systems to attack. We urge everyone who has not yet done so to patch up and use a strong security solution to keep themselves protected,” comments Evgeny Lopatin, security expert at Kaspersky.